On the Internet, no one knows you’re a dog.
But if Strong Customer Authentication (SCA) delivers on its promise, in the UK from 14th March 2022, that may no longer be true.
If every bank and payment service provider follows this new directive to the letter, every hound with ill intent will be scattering back into the shadows.
And yet, inevitably, as is the way with the implementation of all new directives, what we have already seen since SCA was first tabled as part of the second Payment Services Directive (PSD2) back in 2016 (yes, you read that right, it has taken five years!) is confusion, disruption and little agreement over what is and isn’t required to stay within the letter of this new law.
None of which really matters right now because the Financial Conduct Authority, as the prevailing regulatory authority in the UK, is about to start checking for and enforcing compliance.
If your business or institution is affected by this law, the ONLY thing that should concern you is whether YOU’VE done enough to ensure that, when March 14th, 2022 comes around, you’ve done enough to stay well away from breaching it (if you’re still unsure whether you’ve taken sufficient action in this area, don’t wait – CONTACT US for a a confidential review.
This is not an area in which being on or close to the line is advisable.
Worryingly, anecdotal evidence suggests that, if you’re reading this with a vested interest, it’s fairly likely that you’re NOT as prepared as you might believe.
More on that in a moment, but first let’s do a quick recap. Just in case you’re still hazy on some of the details.
What is Strong Customer Authentication (SCA)?
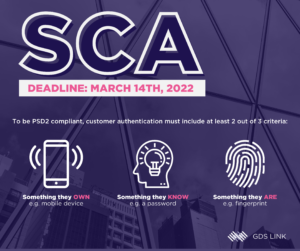
A key element of Payment Services Directive Two (PSD2), SCA is enshrined in Regulatory Technical Standards that require banks and other payment service providers to use at least two authentication factors when taking payments or providing customers with access to their accounts.
The SCA requirements for e-commerce in respect of online and mobile banking formally comes into force in the UK on March 14th, 2022.
How is “Authentication” defined by PSD2?
At the time of writing, many remote transactions are completed simply by checking whether a credit/debit card or identification is real (validation) and whether it matches the person presenting the information (verification). Authentication takes this process a step further by requiring two distinct forms of identification from a consumer to prove they are the person they are presenting themselves to be.
What types of authentication are required?
Authentication can be in the form of either…
- Customer Knowledge: A pin, password, name of the first pet, etc.
- Customer Possession: A phone, security token, pin-generating app, etc.
- Customer Inherence: Face recognition, behavioural biometrics, fingerprint, etc.
Crucially, under SCA, authentication must include at least two of these three elements.
Are any business or transaction types exempt from the SCA?
Yes, however exemptions as defined in the directive get very complicated very quickly.
For example, while transactions under 30 Euros in value are exempt, repeat purchases by a single customer may eventually trigger a requirement to carry out an authentication check.
Industries with historically low levels of fraud may also be exempt, but only for transactions up to a value of 500 Euros.
In short, it would not be sensible to attempt to sidestep the issue solely through exemptions.
Are there any downsides to SCA compliance?
Potentially, yes.
While consumers, when asked, will always claim they want maximum possible security for their online and remote transactions, their irritation over additional authentication steps suggests there are limits on what they are willing to entertain.
For high volume businesses, additional layers of authentication will likely result in a noticeable increase in abandoned shopping carts or app deletion.
There’s a sweet spot that vendors are going to need to find between satisfying the SCA directive, and not irritating consumers through excessive levels of authentication.
Is there a “Best Practice” solution to be SCA compliant?
No, but you’d be forgiven for thinking so given how most banks and businesses are approaching this. Whilst the international card payment schemes have espoused the use of a digital certification solution known as “3D Secure”, this requires a certain version to be adopted to be fully effective and it’s not the only game in town; other SCA compliant solutions are available via other Payment Initiation Services, such as Apple Pay, Google Pay and others. None of which is helpful for non-card payments (GDS Link, in addition to providing consultation in this area, also creates bespoke fraud solutions – Click here to download our Solution Overview.
Which brings us back to our earlier assertion that most institutions are not as prepared as they’d like to believe.
This is because a significant number of UK organisations are intending to use one-time passcodes sent to the consumer through their phone as their main, and sometimes only, method of authentication.
This is understandable given that the technology is well-established, readily available, and in many cases already being used. It’s easy to assume that if you have this method of authentication already in place, you’re all set and don’t need to take any further action.
And THIS is where, we believe, the biggest weakness in SCA lies.
Always remember that fraud is an arms race between the bad actors and the banks. The very fact that one-time passcodes sent to a phone number has been around for so long should be a warning sign that it also has weaknesses that fraudsters have learned to attack.
Specifically two that are areas of concern…
1) Man in the Middle
If the consumer has, for example, malware on their device, it’s possible for a fraudster to attack the security of the channel itself.
The consumer can complete the secure pass-code authentication, at which point the fraudster can step in and intercept the transaction, and in some instances even repurpose the customer’s authority to another purchase.
2) SIM-Swapping
If a fraudster knows your password, or is otherwise able to successfully impersonate you with your telecoms provider, it’s possible for them to transfer your phone number to another device. This allows the criminal to receive the requested one-time passcode and circumvent the authentication controls the banks have come to rely on.
You know the old story about the two friends being chased by a bear?
One says to the other, “Why are we running? We can’t outrun a bear.”
The friendly replies, “I don’t have to outrun the bear, I just have to outrun you.”
Once everyone is using SCA, the fraudsters won’t go home, they’ll just focus on the weakest points of attack. It’s a nihilistic point of view, but it can’t be denied that the best way to avoid fraud is simply to have above-average security.
One-time passcodes may not be the weakest authentication method out there, but they’re a long way from being the strongest.
This doesn’t mean you shouldn’t use one-time passcodes, but if you want to stay ahead of the game you need to look at bolstering it with a second layer of protection, such as inherence. See my separate blog on behavioural biometrics for an example of this.
If you’re a retail (consumer) bank or a merchant (acquiring) bank, and you have even the slightest doubt about the strength of your authentication, or how well it will measure up to the new SCA directive, GDS Link can help. Book a free demo today to learn more.
We can provide consultation in the area of SCA compliance, or even a bespoke fraud solution to ensure your authentication measures are as strong as they need to be, not just to stay within the law but also to provide maximum protection for your business and reassurance for your customers.
If SCA does produce the intended result, of figuring out who on the Internet is a dog, the rabid canines of this world won’t go into hiding…
They’ll simply improve their disguise.
So, whether you already have a strategy for SCA compliance come March 14th, 2022, or you’re still putting one together, look again with a long-term mindset and you’ll save yourself some very unpleasant headaches in 2022.









